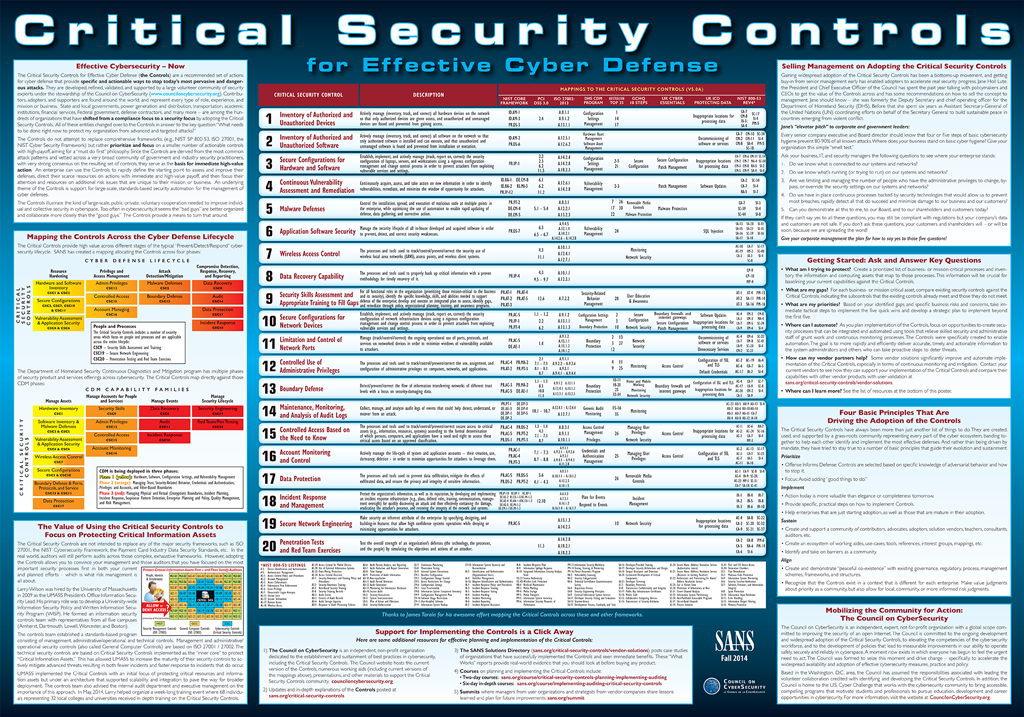
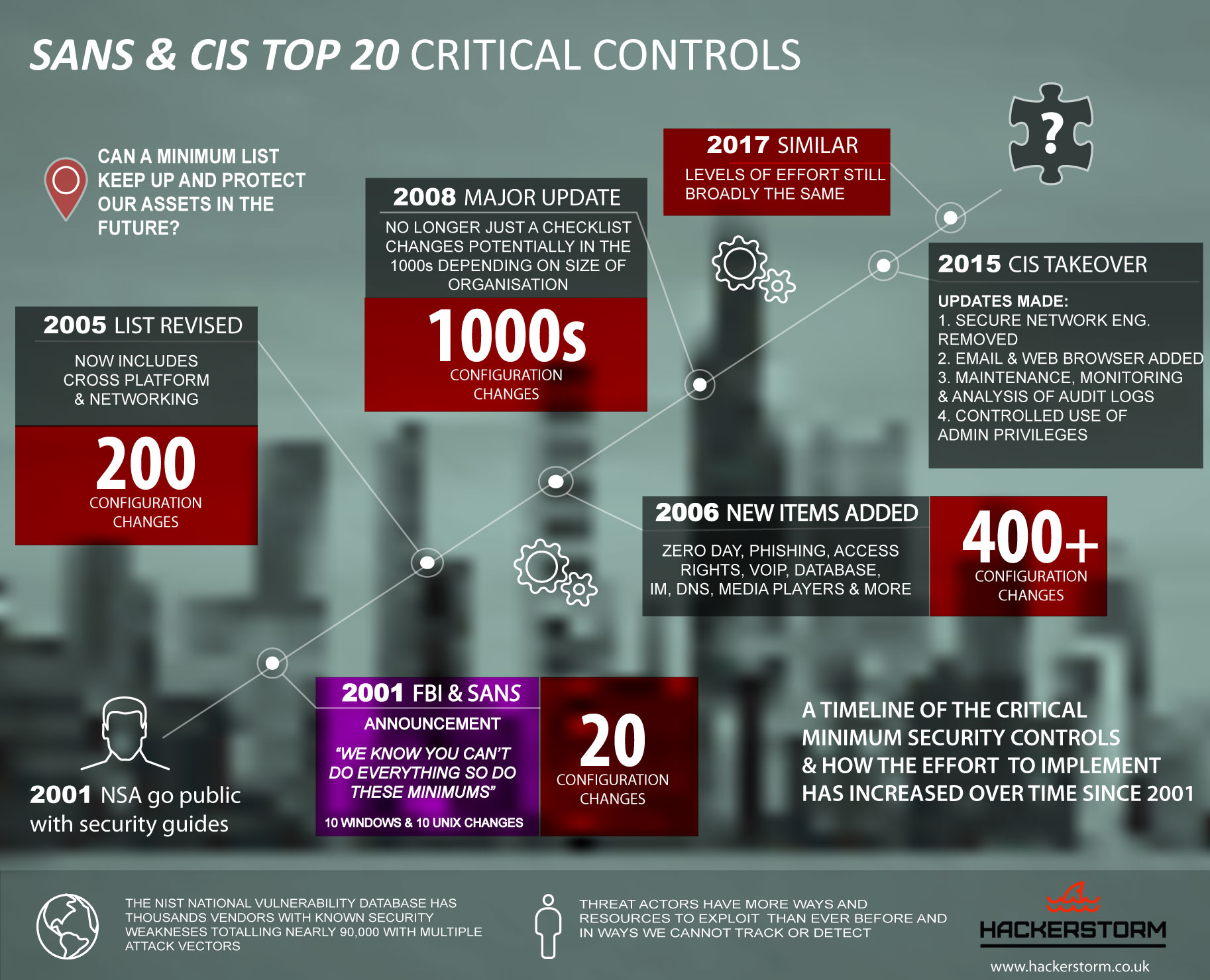
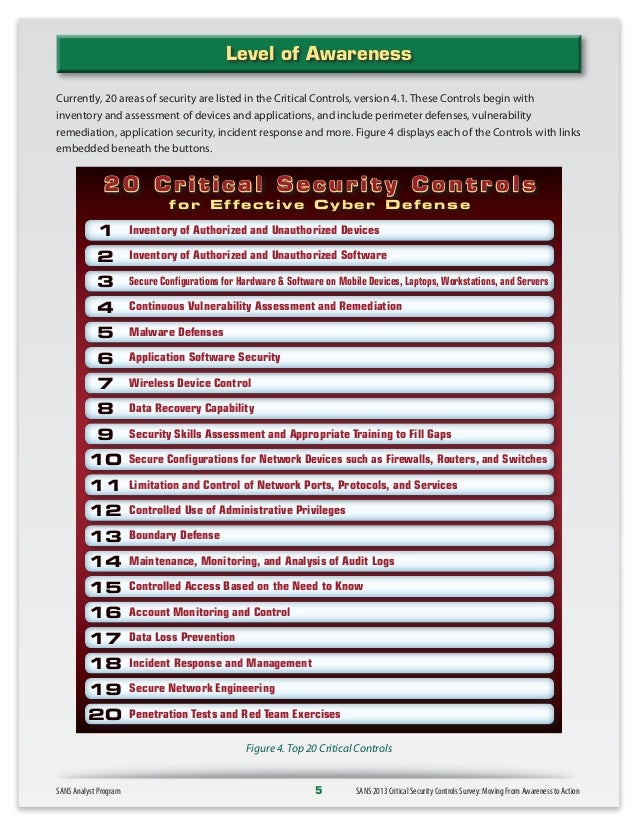
Michael Fisher Twitter પર: "What are the top 20 controls for a healthy network #Security posture? {Infographic} #CyberSecurity #infosec #education #DevOps #Malware #databreach #Pentesting #IRP… https://t.co/Jw0Wr96CSm"
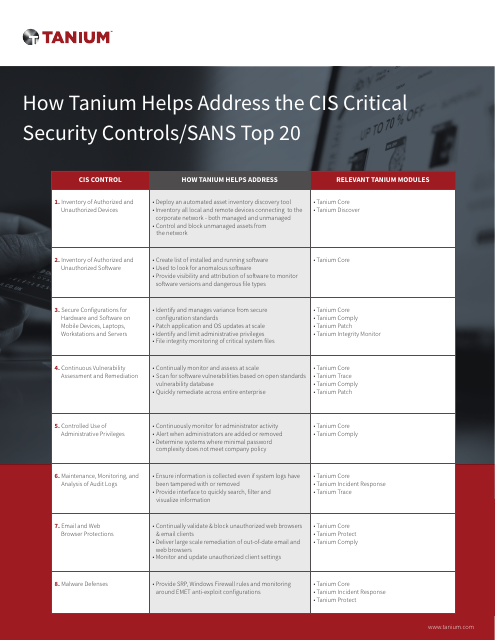
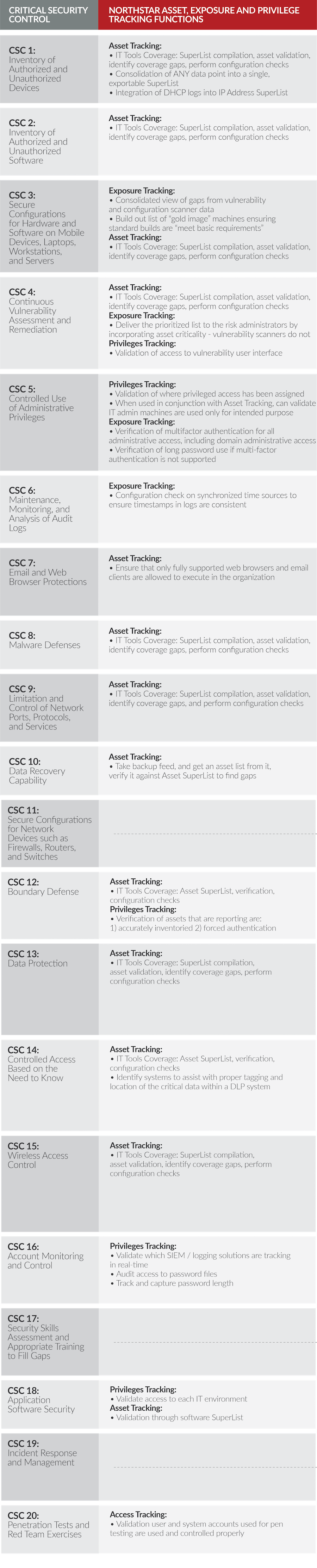
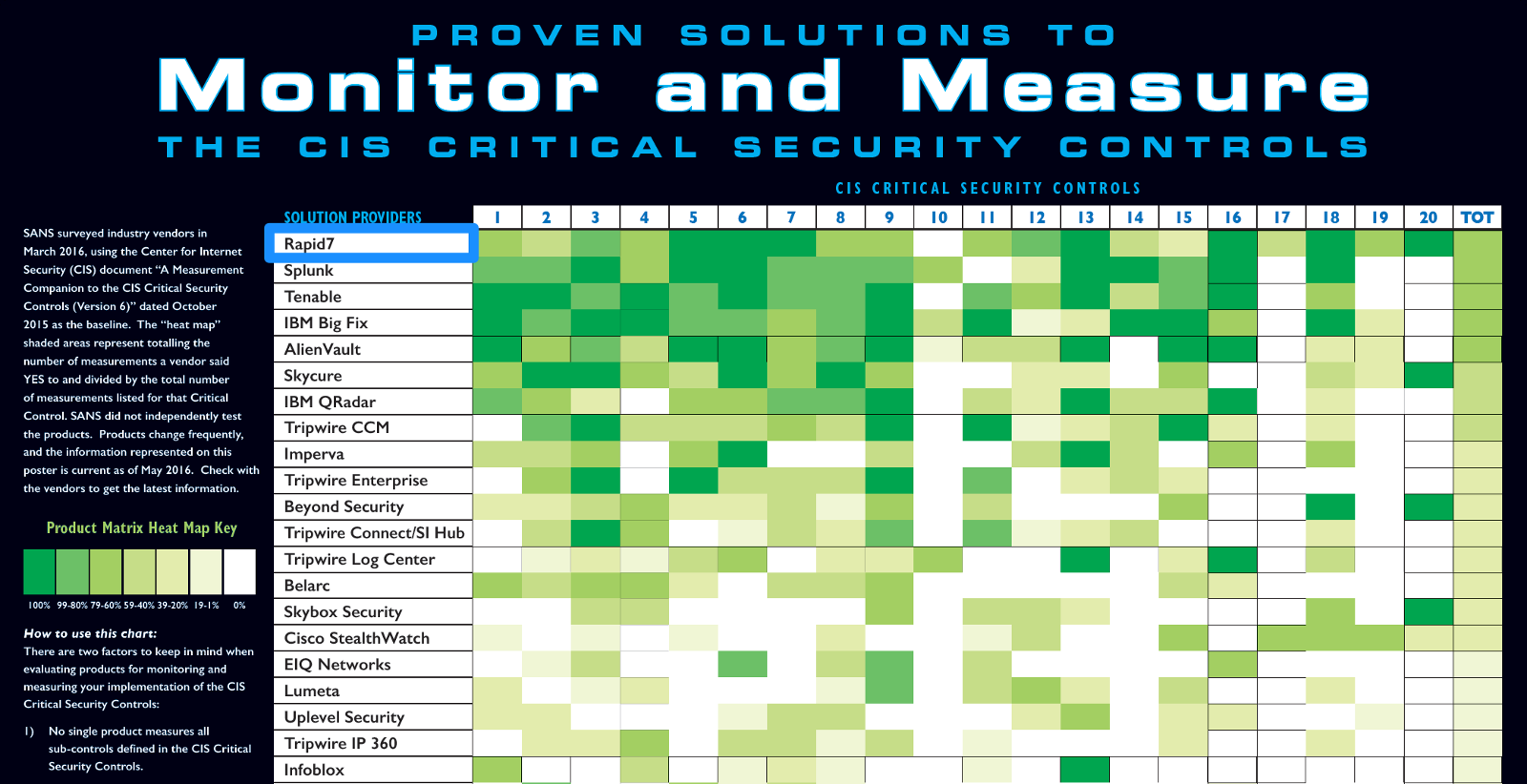
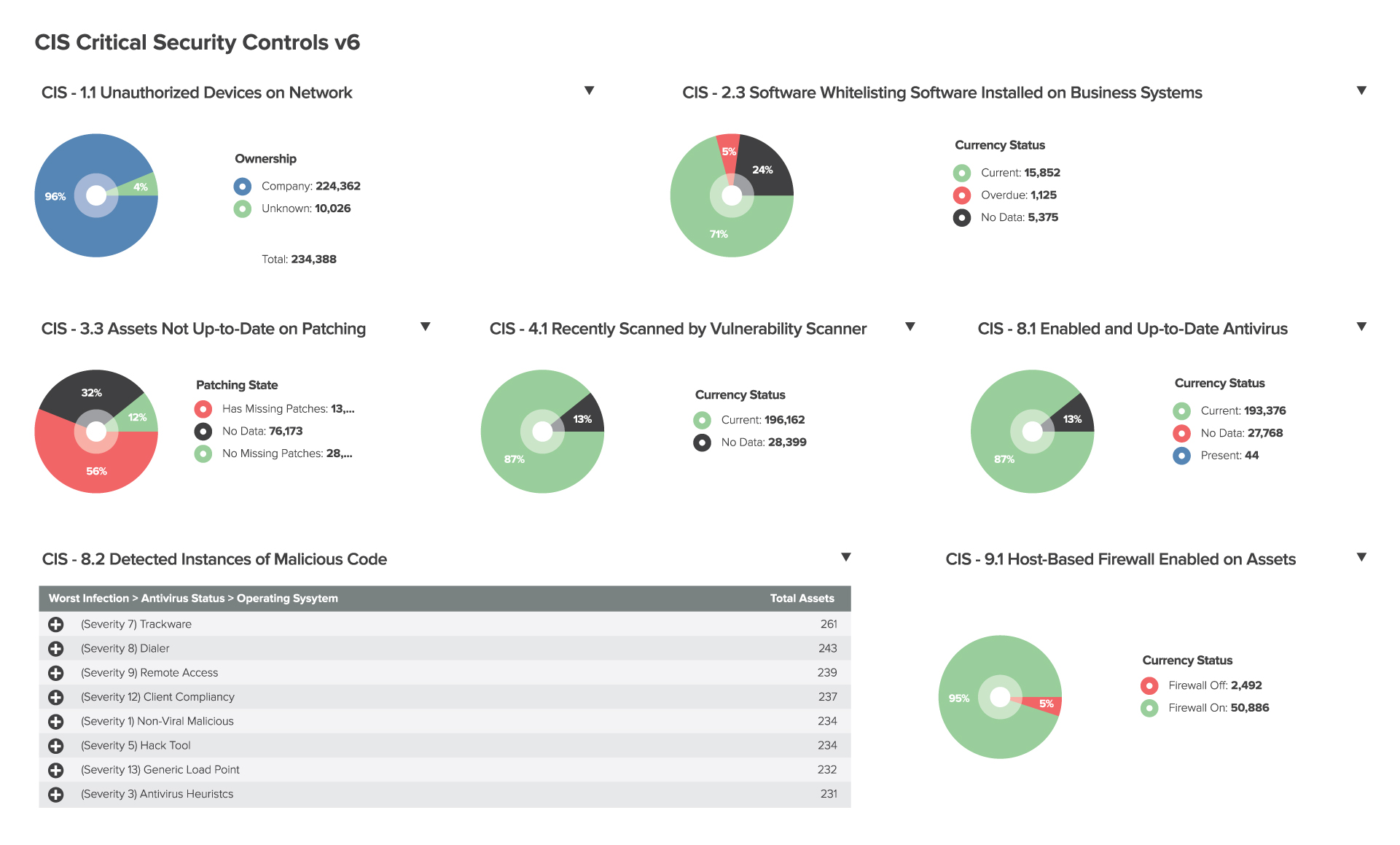
How Tanium helps address the CIS Critical Security Controls/SANS Top 20 | Cyentia Cybersecurity Research Library